Subscribers Only
 Subscribe to Maine Antique Digest Today!
Subscribe to Maine Antique Digest Today!
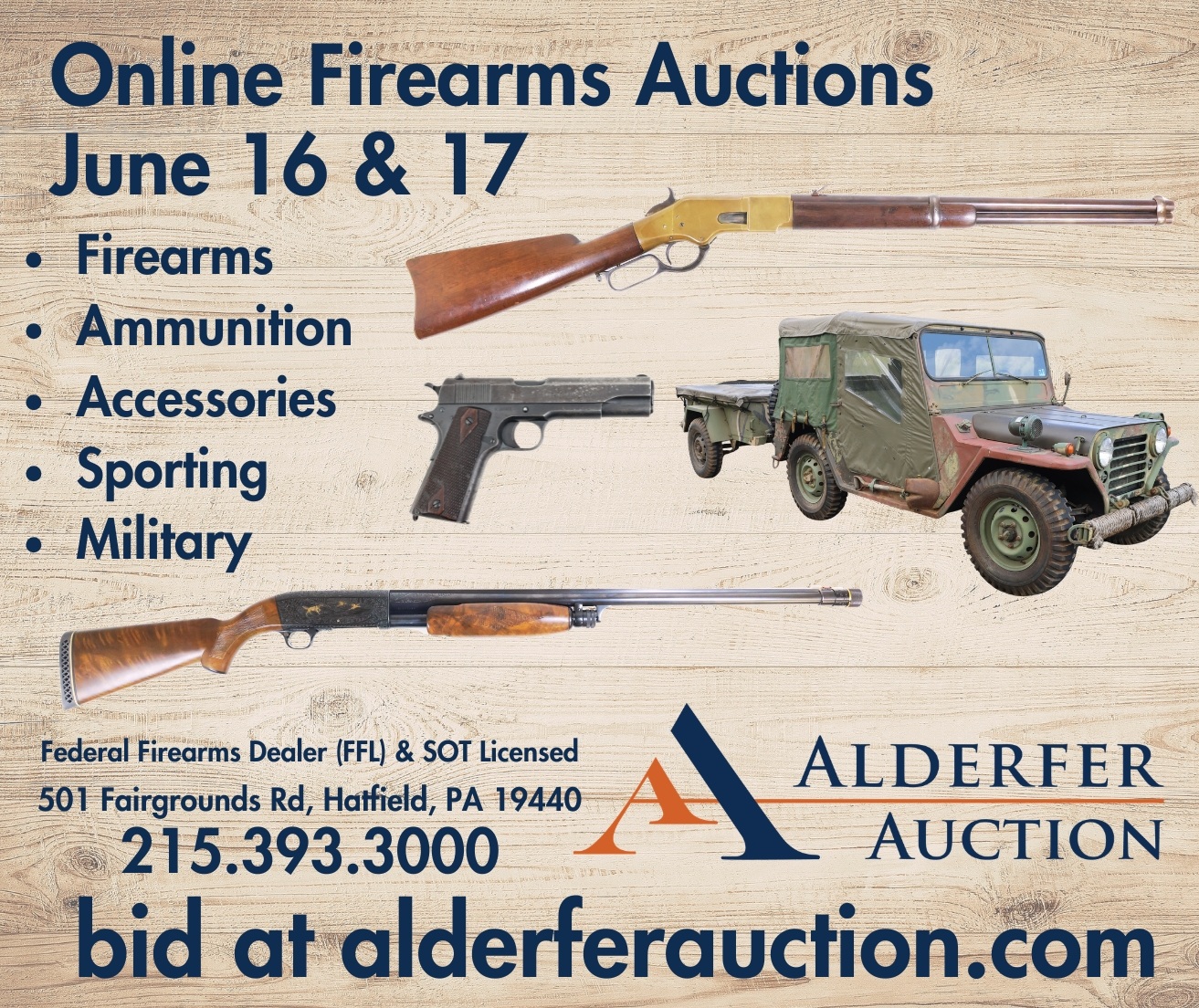
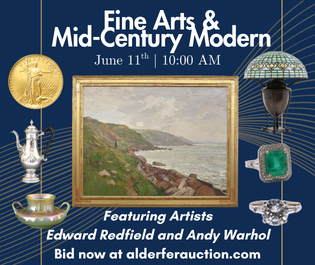
Published monthly, Maine Antique Digest covers the antiques and art market, particularly Americana. Each issue is packed with prices and pictures from shows and auctions from across the United States and Canada. Other features include market news, previews of exhibitions, book reviews, letters to the editor, club and association news, obituaries, and more. M.A.D.’s annual Antiques Trade Directory is published in December.
Subscribers have complete access including full digital editions, past issues, an auction prices database, and much more.
To subscribe, click here
https://simplecirc.com/subscribe/maine-antique-digest
*****